Microsoft Defender for Cloud Integration for Code-to-Cloud Risk Visibility Reaches General Availability
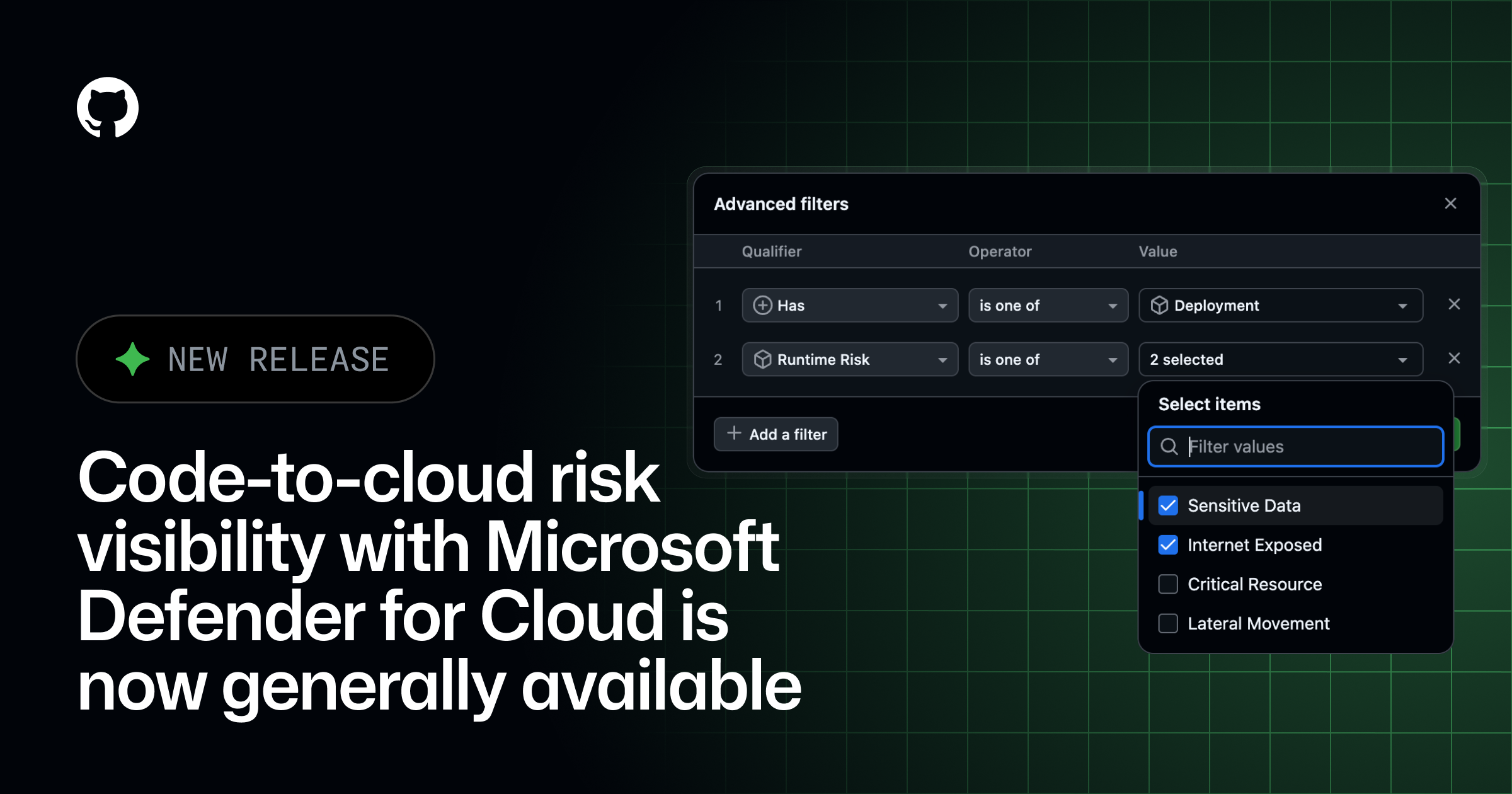
This integration enables engineering and security teams to trace cloud vulnerabilities back to the specific repository and line of code that introduced them. By correlating GitHub Advanced Security findings with Microsoft Defender for Cloud, organizations can prioritize remediation based on the actual runtime impact and exposure of their cloud resources. This unified visibility reduces the time spent investigating security alerts and helps prevent vulnerable configurations from reaching production environments. Developers can now view security insights directly within their existing workflows while security administrators maintain a comprehensive view of risks across the entire software development lifecycle. Organizations should review their existing GitHub and Azure configurations to enable these features and ensure that the appropriate permissions are granted for cross-platform data sharing. Detailed setup instructions and compatibility requirements are available in the official documentation provided by GitHub and Microsoft.
Related tools
Recommended tools for this topic
These picks prioritize high-intent tools relevant to this topic. Some links may include partner or affiliate tracking.
High-value hosting and deployment path for frontend and cloud readers.
View VercelStrong cloud alternative for startups and developer-led infrastructure decisions.
View DigitalOceanA strong security and edge platform match across CDN, Zero Trust, and app protection.
View CloudflareComparison
| Aspect | Before / Alternative | After / This |
|---|---|---|
| Risk Context | Security alerts isolated to either code or runtime | Unified visibility correlating code flaws with cloud risks |
| Remediation Path | Manual tracing from cloud alerts to source code | Automated mapping to specific repositories and authors |
| Prioritization | Based on static severity levels alone | Informed by runtime exposure and business criticality |
| Workflow | Switching between multiple security dashboards | Integrated view within GitHub and Defender for Cloud |
Action Checklist
- Enable GitHub Advanced Security for target repositories Required to generate the code-level security data
- Connect GitHub organizations to Microsoft Defender for Cloud Requires administrative permissions on both platforms
- Configure the DevOps security connector in the Azure portal Ensures data synchronization between platforms
- Review and assign security roles for cross-platform visibility Grant access to security teams to view integrated insights
- Validate data flow by running a test security scan Ensure alerts are correctly mapped from code to cloud resources
Source: GitHub Changelog
This page summarizes the original source. Check the source for full details.