GitHub Secret Scanning Integration with Model Context Protocol Server Reaches General Availability
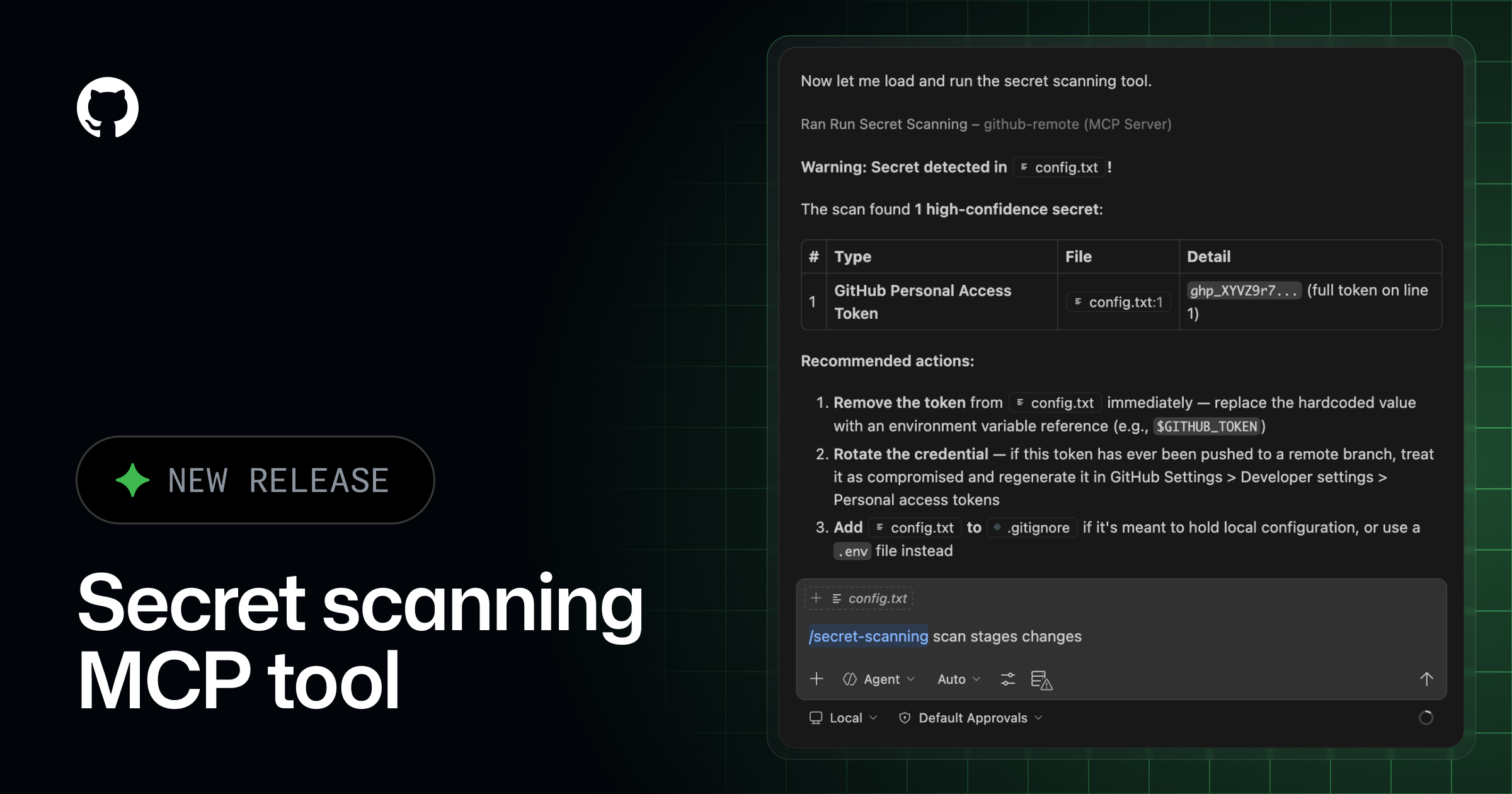
GitHub has announced the general availability of the Secret Scanning integration via the Model Context Protocol server. This release enables AI agents and large language models to interact directly with GitHub secret scanning data in a structured and secure manner. By leveraging the Model Context Protocol, developers can now integrate security alert workflows into their local AI-powered development environments.
Related tools
Recommended tools for this topic
These picks prioritize high-intent tools relevant to this topic. Some links may include partner or affiliate tracking.
Strong fit for AI, backend, and frontend readers looking for an AI-first coding workflow.
View CursorHigh-value hosting and deployment path for frontend and cloud readers.
View VercelA strong security and edge platform match across CDN, Zero Trust, and app protection.
View CloudflareComparison
| Aspect | Before / Alternative | After / This |
|---|---|---|
| Integration Method | Manual API calls or Webhooks | Standardized MCP Server |
| AI Interoperability | Custom prompt engineering for context | Native context sharing via MCP |
| Workflow Automation | Fragmented across different tools | Unified agentic security remediation |
Action Checklist
- Install the GitHub MCP server package Ensure your environment supports the Model Context Protocol specification
- Configure GitHub authentication tokens Use fine-grained personal access tokens with secret scanning read access
- Connect your AI agent or IDE Update local configurations for Copilot or other AI tools to recognize the MCP endpoint
- Verify alert retrieval functionality Test with a non-critical repository to confirm permissions are correctly scoped
Source: GitHub Changelog
This page summarizes the original source. Check the source for full details.


